So, You're a Manager Now
April 29, 2022
Transitioning from being an Individual Contributor (IC) to a Manager is one of the most difficult shifts any person may make in their career. This represents a recognition of growth as well as a drastic change in responsibilities. Like becoming a parent it’s something that none of us are ready for until it happens, but somehow, many of us will succeed. The difference in success depends on how much effort and focus you give your new role as well as the support and tolerance you give yourself.
read moreA Mixtape in 2022
February 4, 2022
I had the idea to create mixtapes, real, vinyl-to-tape, analog, lift-and-drop-the-needle, mixtapes, for my friends during a drive back from Montana after Thanksgiving. There’s something lost in the digital music era, where every song of every album from every artist is available at any moment at a click of a button. The ability to create a digital playlist, to be able to listen, reorder, or swap songs at a whim is convenient, it loses what drew me to vinyl in the first place, a purposefulness and intention to music.
read moreThe Middle Path of Planning and Reflection
December 28, 2020
Thinking about the future or past is an important practice, but we must be careful to not to take either too far. Buddhists call this the Middle Way or the Middle Path. Taking any practice too far can be detrimental: over-indulgence or self-mortification is not ideal. We can apply this same goal to planning and reflection.
Think about the future too much and it can become anxiety or anticipation for something that may never come, but think about the future too little and you’ll be blind sided by predictable events.
read moreMicromanagement and Trust
July 31, 2020
If you ask 100 employees if they like to be micromanaged 90 of them will say no, and the remaining 10 will walk away in disgust at you having the gall to ask the question. Micromanagement is so bad it’s almost synonymous with bad-management. If we all know it’s a bad choice, then why do managers do it?
I’ve been able to hire, promote, and observe quite a few managers and leads over my career.
read moreOn Giving Advice
March 9, 2020
A friend of mine, Arvind, writes a blog called “myotherramblings.” It’s a place where he can write about anything he’d like to. Recently he wrote a post on The Dark Side of Advice, I recommend you read it. I’ve often felt similarly, “if people aren’t going to do what I say, why did they ask me for advice!” This post got me thinking about another facet to giving advice. This post was originally an email directly to them, but I felt like it was helpful enough to post here.
read moreEmergency Preparedness During Coronavirus Frenzy
March 5, 2020
In the midst of Coronavirus frenzy I decided to bring up a blog post I’ve been slowly writing for some time now. I am what I would consider a tentative “prepper” I like to be prepared for the threats that I think are most likely without going crazy and building a nuclear bunker in my back yard. I think there are a few things that we can all do to improve our preparedness that have little effect to your day to day life, but can significantly increase your comfort and decrease your stress in an emergency.
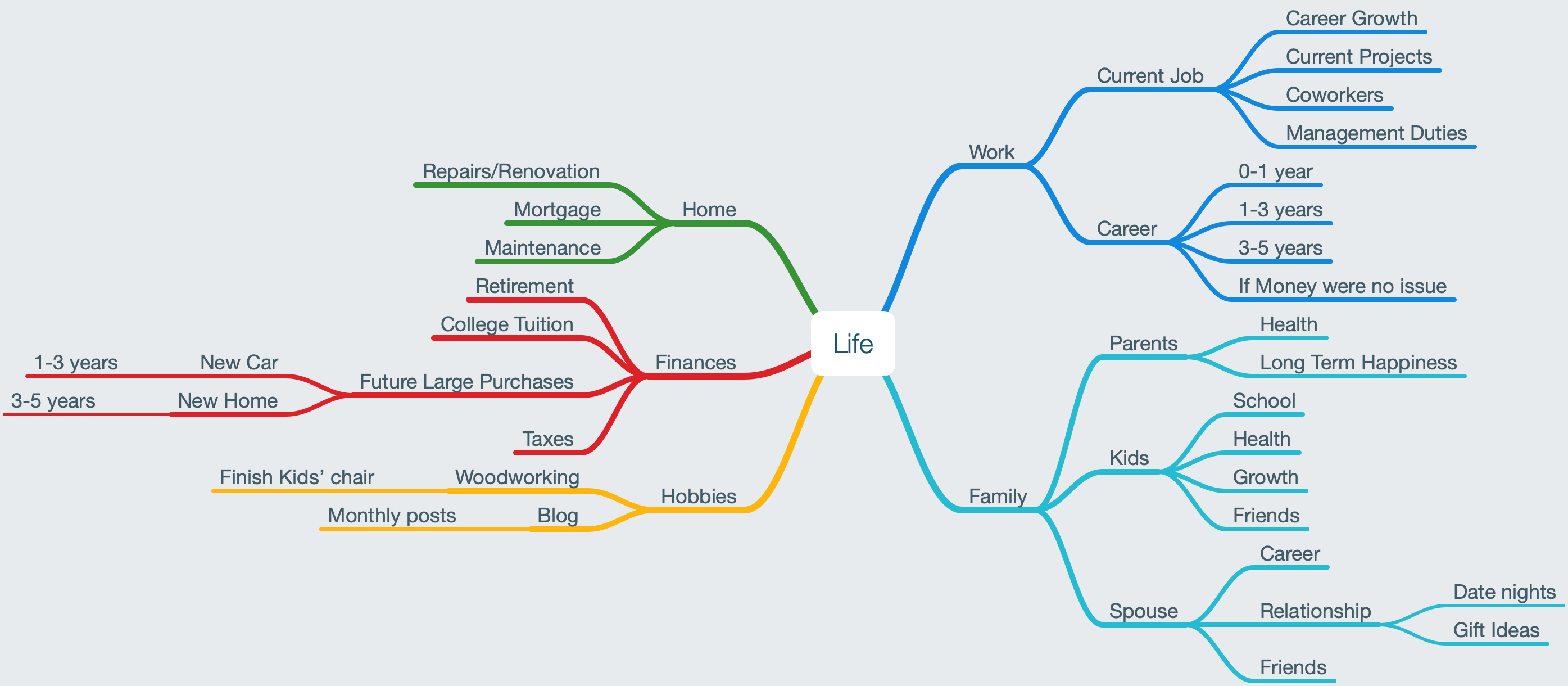
read moreMind Map Your Life
February 19, 2020
Recently there have been a lot of things going on in my life. So many that I started to find it difficult to keep track of everything. I needed a way to organize my thoughts so I could feel comfortable that things weren’t slipping through the cracks and so I could organize and attack my concerns.
A computer can slow down when you have lots of programs running, even when they’re in the background or not being currently worked on.
read moreStart With the Hard Part
October 25, 2019
I like Seth Godin’s blog I recommend you check it out. He writes daily, so it can be overwhelming, but there are really some good nuggets in there.
Today was about identifying the hard part of a project. I think that’s important, but you should start with the hard part whenever possible.
Tackle the biggest, ugliest part you can find. Better to get it done up front that sinking a bunch of time and energy into the project only to learn that you’ll be blocked later down the road when you get to the hard part.
read moreDelight in the Details
October 23, 2019
In trying to understand something we can often fall into a pattern of mapping the new thing to something we already know. This is a great way to get a foundation for understanding but it’s a shortcut and it’s important to dive into the details for better understanding and more excitement.
When you generalize that loses all the interesting parts. Look for what’s exciting and new in new things to learn and resist the attraction to generalize and blur the subject.
read moreIntroducing ReThink Security
August 21, 2019
Recently Jason Taylor and I started a new side project, ReThink Security. The purpose is to share the insights that we’ve built up over the past two decades in the security industry. During this time we’ve spoken to countless people in the security industry, help move teams of individuals forward in security maturity and worked with organizations ranging from the largest in the world to weeks-old startups looking to minimize security missteps.
read moreNewsletter & Recommendations
June 6, 2019
Recently I’ve noticed that I prefer to receive updates from my favorite blogs in email. If you feel similarly I’ve signed up with Mailchimp to deliver my posts via email. Of course I’ll never share your information with anybody else, and if you unsubscribe Mailchimp will handle that quickly and thoroughly.
If you’d like to sign up for the newsletter you can do that here on mailchimp
If you prefer rss, that’s still available here at the rss link.
read moreTake a Moment
June 3, 2019
There are very few things in life that require an immediate response.
I wrote earlier about how you can Triage Decisions to try to undersatand how much effort you should spend on each decision. I would add to that only to say that however long you think you should take, you can almost always take more time.
You can take a moment to collect your thoughts, to calm your emotions, or to see something from a different perspective.
read moreTriage Decision Making
May 16, 2019
Not all decisions require the same amount of time to think through, but some high impact decisions warrant your time, energy, and effort to make valuable decisions.
To help understand how much energy you should put into a decision think about the impact it will have and the ease in which you can change it.
If the decision will have wide reaching impact and cannot be easily changed do not make the decision on the spot in real time.
read moreShow Your Work
April 26, 2019
There’s a fine line between bragging and letting people know what you’re doing. Many times in a work setting it is important to make a little more noise about yourself than you think you should.
Letting people know what you’re up to, especially bosses and peers can help build respect, trust and ultimately help your professional progress.
Tell people when you’re proud of something, ask for help when you stumble, share knowledge that you find interesting, communicate more.
read moreGetting Back Up
March 7, 2019
Habits are important, but restarting is more important. You will forget to work out, fail at your diet, upset a friend or coworker, or make a million other mistakes.
The quicker you get back up and restart the easier it will be. The longer you wait the more painful it will be to start again.
Next time you skip a run start get back into the habit quickly. If you make a mistake, own up to it quickly and start work again.
read moreMax Out vs. Continuous Development
February 28, 2019
There’s a mental difference between thinking that something can be maxed out versus being constantly improved and developed. If something can be maxed out there is an end. This end can become a goal, which can be helpful, but it can also be limiting. If you feel you have maxed something out in your life if can also be a source of ego. Targeting maxing something out can be dangerous and ultimately discouraging.
read moreMental Diet and Exercise
February 19, 2019
Recently I noticed an old pair of pants were a little tighter than I remembered them being. It was easy for me to jump to the conclusion that I either needed to accept my new form and buy new pants or I needed to adopt a better diet and focus on my exercise. It’s easier to eat junk food and skip the gym, it’s tough to make lifestyle changes, but for me that was what I had to choose to do.
read moreAsking for Help Part 2 - Alerting
February 4, 2019
I realized in my first part of Asking for Help that I didn’t put a fine enough point on some of the points I should have made when asking for help.
Alerting falls into a greater category of communication. Alerting, or maybe we can call it “Struggle Signaling,” can help others know that, while you’re not yet ready to call it quits and ask for help, things aren’t going as smoothly as you’d like.
read moreHigh Water Mark
January 17, 2019
You have experienced what it feels like to be at your best. Those moments when you are focused and clear-headed. Maybe you were on a deadline, got into the flow of work, or truly loved what you were working on. Those moments are your high water marks.
Understanding what is possible and cultivating those moments is a great way to help capture more moments like that.
Next time you feel at your best take note of what is going on and how you got to that state.
read moreWho Do You Want to Be
January 11, 2019
There are many questions that you can ask yourself to help frame the person you want to grow into. These questions can be standard ones like “Where do you see yourself in 5 years” and “What’s important to you?”
There’s a difference between who we want to be internally, and how we want others to perceive us.
Who do you want to be? For the first question, think about who you want to be in your core.
read morePresentation Tips
January 4, 2019
I recently had the privilege of having Montana Von Fliss give me some pointers on a talk I delivered to a client. She was there in another capacity, but never one to let an opportunity for growth slip by, I grilled her on what I could do to improve my presentation style.
Hook the audience with a story Start with “So there I was…" Then drop into the middle of the story
read moreAsking for Help
January 2, 2019
When asking for help I always try to think about whether the person who I am asking can answer my question off the top of their head or if it’s something that will require them to do a bunch of research into.
If it’s off the top of their head, ask immediately. Better to get yourself unblocked sooner rather than later. If it’s the kind of thing that you can do your own research for or come to the table with your own potential solutions for that makes everything easier and faster.
read moreChina Hijacking the Internet
October 29, 2018
(image source Demchak)
ZD net posted an article that talks about China intercepting internet traffic to collect data, which sources data from research done by Demchak.
I think it’s reasonable to say that all traffic is being hijacked and logged. Assume the internet is a public forum and corporations, nation states, and other attackers are collecting every bit of information that is available about you.
At the top you have advertising agencies like Facebook and Google tracking what you look at on the internet, and the bottom you have these types of attacks which look at the traffic at a lower level.
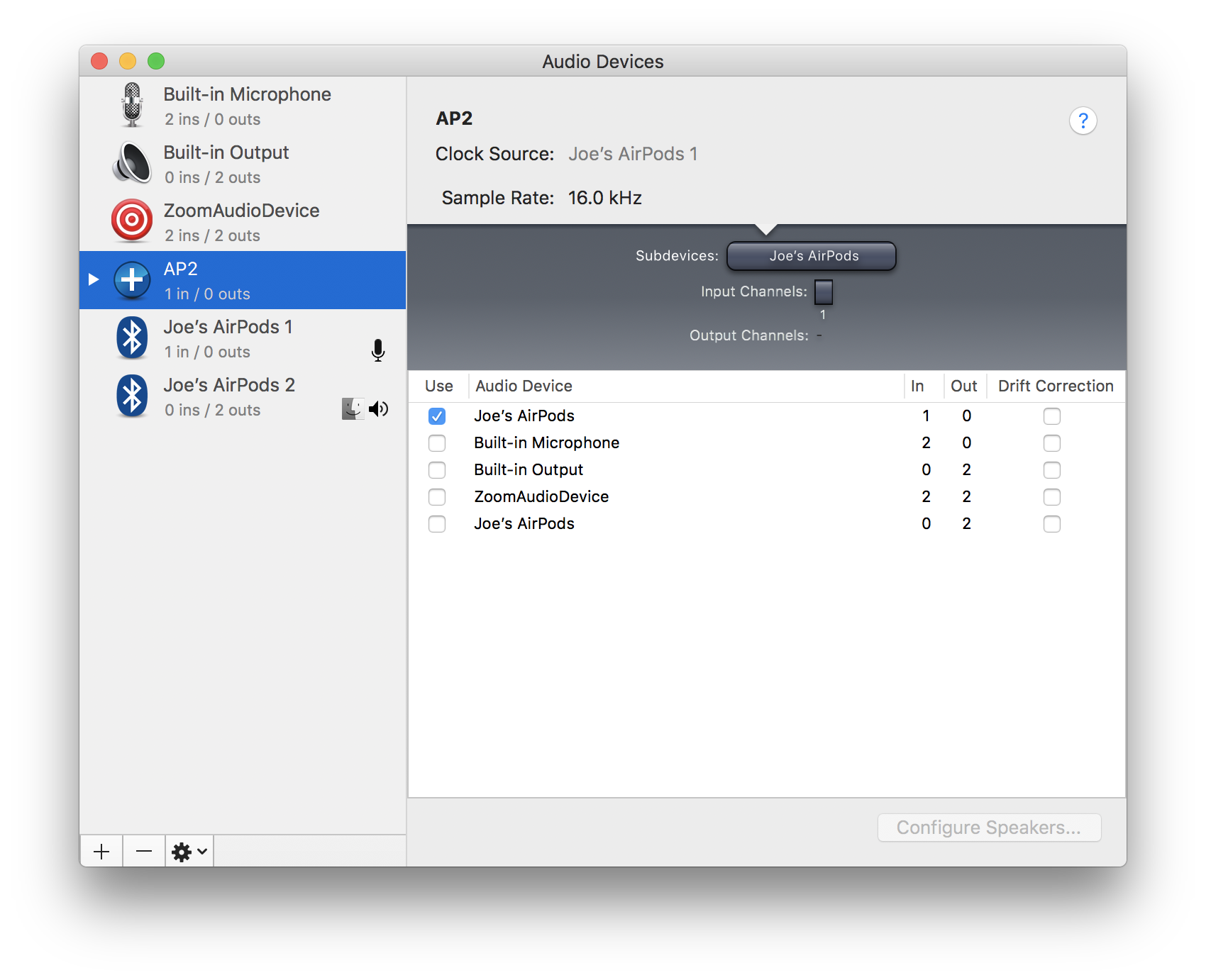
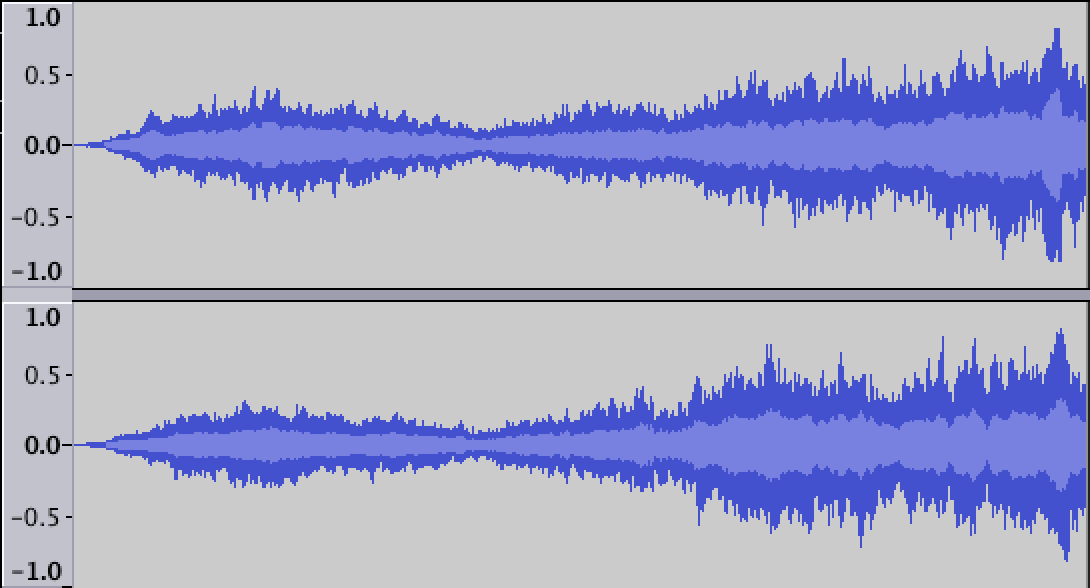
read moreRecording Audio with AirPods in Imovie
September 6, 2018
By default iMovie doesn’t recognize AirPods as a recording device. This probably has to do with Bluetooth latency or quality, etc. but if you want to force iMovie into using the AirPods as an audio in device you can do it by creating a new Aggregate Device with the Audio Midi Setup Tool.
First launch the Audio Midi Setup app, and click the + in the bottom left of the window.
read moreActive Decisions
August 22, 2018
Decisions will be made — by you, or for you.
You can either take active participation in those decisions and decide the direction of your future actively or allow them to happen without your involvement or influence.
Not all decisions matter enough to your happiness or wellbeing to warrant the time and analysis that making an active decision requires. However, big things like the direction of your career, the people you spend time with, your health, and other areas of your time and life can make a big difference.
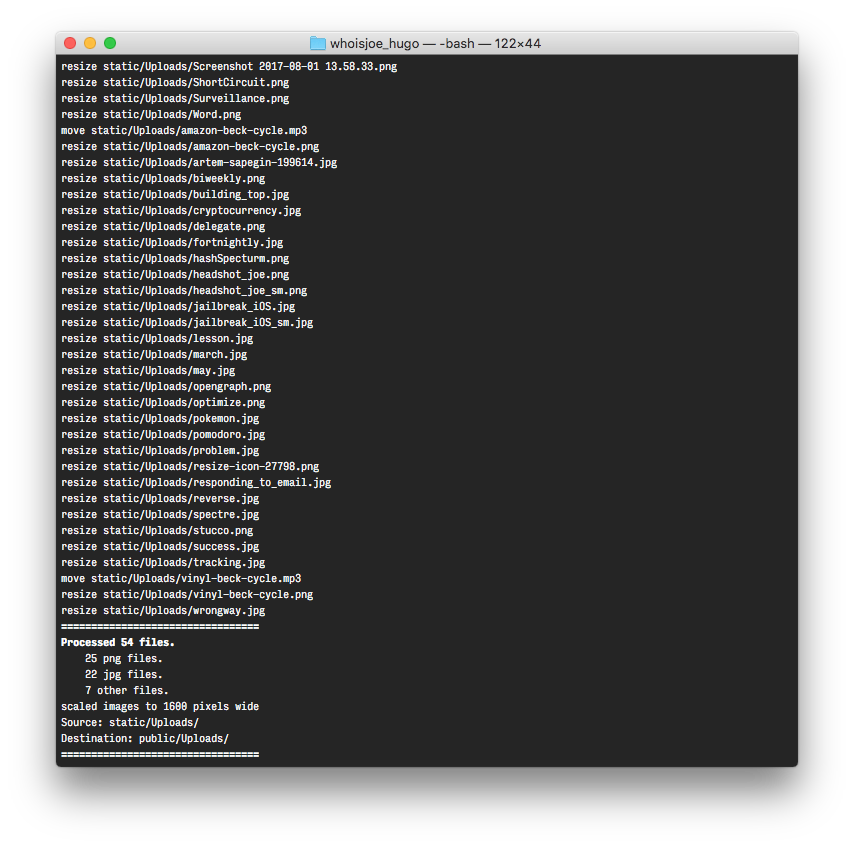
read moreCreate/Publish Scripts
August 8, 2018
In order to make creating and publishing quicker and easier I created a couple of little shell scripts to help me along my way. I have a hard time remembering all the little switches and commands to publish and I hate making little mistakes each time I try to do something quickly. The answer is simple, automate the monotony away!
The first script new.sh creates a new post in the post directory.
read moreSpecialize or Do Not Specialize
August 8, 2018
In my industry I’ve found that you can be successful by committing to being a specialist or by committing not to specialize. People stumble, struggle, fail, or get burned out when they try to do both or can’t transition from one to another.
As people become more senior in their careers they naturally take on more and more responsibility, this is a great way of increasing influence and capabilities. Focusing on one thing and trying to learn that one thing better than anybody else is what a new employee will do to be exceptional at their job.
read moreExactis Breach
July 26, 2018
I recently learned about a new Exactis data breach. No passwords were compromised, but much of the information that would be used in a social engineering or phishing campaign was collected by Exactis and lost in this breach. The data breach included 340 Million records, so it is also likely that your personal information may be lost. According to haveibeenpwned:
The leak contained multiple terabytes of personal information spread across hundreds of separate fields including addresses, phone numbers, family structures and extensive profiling data.
read moreOptimizing Images
July 19, 2018
I started down a little bit of a rabbit hole when I wanted to optimize and scale the images on my site. As you can see there are a lot rather large images on my site, which I like the look of. I just don’t like that some of them were greater than 5MB each!
I started out by searching for a basic bulk image processing tool. I wanted something that wasn’t bloated, janky, or broken.
read moreWhat I Track
July 3, 2018
I’ve recently added basic Google Analytics tracking to this site. This is just to give me a sense of how many people are looking at my site and to understand what articles and topics are popular. I’ve disabled Demographic and Interest Reports and other enhanced tracking features which can be invasive.
In order to do this analytics I’ve included a snippet of JavaScript on the site, which you can find in the header of every page.
read moreWhat I’m Thinking About May
May 5, 2018
Safety, Security, and Privacy Safety, Security, and Privacy continue to be merged together as IoT increases its reach into new devices. IoT devices are being develope with little security in mind, these devices continue to be attacked successfully. I attended a talk at ZonCon by (Senrio) in which their VP of Research outlined the many, many issues they’ve discovered in connected medical devices. Microsoft released Azure Sphere which aims to help their customers build more secure IoT devices with easy Azure connectedness and a standard Linux based platform.
read moreWhat I’m Thinking About March
March 2, 2018
Lots of lost certificates 23,000 HTTPS certificates axed after CEO emails private keys | Ars Technica The email was sent on Tuesday by the CEO of Trustico, a UK-based reseller of TLS certificates issued by the browser-trusted certificate authorities Comodo and, until recently, Symantec. It was sent to Jeremy Rowley, an executive vice president at DigiCert, a certificate authority that acquired Symantec’s certificate issuance business after Symantec was caught flouting binding industry rules, prompting Google to distrust Symantec certificates in its Chrome browser.
read moreWhat I’m Thinking About January
January 10, 2018
Spectre & Meltdown Wow, this is a terrifying vulnerability, which honestly means that we have to decide between an attacker being able to read all the memory on their server, or a 20-40% increase in CPU load. This has massive implications for shared computing like servers, the cloud and other technologies like Docker. A co-worker of mine, Mick, wrote a great blog post on this: https://blog.securityinnovation.com/spectre-meltdown-vulnerabilities-cutting-to-the-chase
AI/ML I’m still thinking a lot about AI/ML.
read moreBuilding a Collaborative & Social Application Security Program
October 9, 2017
It’s no secret that more and more companies are jumping on the Bug Bounty Program band wagon, and for good reason, there is a lot of value to be had there. However, rolling out a Bug Bounty Program (BBP) before you have done your own due diligence can often cause more problems than it solves.
Bugcrowd, one of the largest bug bounty program service providers touts that within the first two weeks a typical company with a new BBP will see 5 critical vulnerabilities, 70 unique vulnerabilities and 200 total vulnerabilities.
read moreLazy Days in the Cloud
August 1, 2017
The cloud brings scalability, reliability and security features that allow companies of all sizes to run their online business efficiently. These powerful capabilities often bring a false sense of a “security is already done” mentality and organizations are prone to take a more relaxed approach to their security efforts. Additionally, while many of the cloud platform features are “built-in”, that doesn’t mean they are optimized for your organization out of the box – they still be analyzed in the context of a larger security strategy and re-evaluated frequently.
read moreDelegate Then Do
July 11, 2017
Being a manager is difficult. It’s sometimes difficult to know what tasks you should do yourself and what you should give to your team. I’ve adopted the Delegate then do methodology for myself.
Delegate everything you can to anybody on your team who can accomplish the task. Do this by default. Give your team the benefit of the doubt, and give them difficult tasks that they’ll have to rise to the occasion for.
read moreSo you want to be a better programmer
June 14, 2017
I get asked sometimes how some people on my team can become a better programmer. I think it's useful to think in terms of different evolutions of the programmer. In the beginning there's a scripter or coder and at the highest level you have an architect. There is much, much more to go into here, but this is a rough framework to plot your skills over time.
Use this to fill in your current skills and to identify key areas of improvement.
read moreProject Success
June 9, 2017
This diagram is an approximation of how I think about iterating toward a goal to increase my likelihood for success. There are a few concepts that I’ve packed into this diagram, so I’ll try to explain here. I’ve also recorded myself drawing this diagram roughly in order of operations on youtube. here.
Step 1: Set a Clear Goal Defining a clear goal and understanding what “Success” looks like is the most important first step.
read moreDon't Short Circuit a Lesson
June 3, 2017
Don’t short circuit a lesson because you think you know what the take away is going to be. Too often we try to map other’s experiences or recommendations to our own and we miss out on new opportunities to grow or learn.
Next time you hear somebody describing something they just learned don’t interrupt with by saying “oh, I know where you’re going” or “I know something similar” instead do two things:
read moreScale Your Solution to the Problem
May 30, 2017
It’s important to Scale your solution to the problem at hand vs. trying to scale the problem to your solution.
By analogy a master photographer knows when to pull out her iPhone and take a quick snap, edit it in-app and upload it to Instagram and when it’s appropriate to break out the $5k camera body and $5k lens, and wait for the perfect opportunity and use Photoshop to edit the photo to perfection.
read moreDigital Currencies
May 24, 2017
I recently got interested in Digital Currencies, such as Bitcoin and others and decided to start learning about what they were, why they’re interesting, and how to invest.
There’s a lot to understand about cryptocurrencies or digital currencies (DCs), and I’m just getting started learning about it. But if you want to learn more a good place to start is https://www.cryptocoinsnews.com which is just a place to learn about what’s going on in the cryptocurrency world.
read moreFortnightly
July 27, 2016
Sorry biweekly, you’ve just been ejected from my vocabulary. I hate to be esoteric in my language and use a word like fortnightly, but when your definition from Merriam Webster has two directly conflicting definitions I simply cannot use that word. Fortnightly it is!
From Grammar Girl:
Semi- always means “half.” You can remember the meaning by remembering that semisweet chocolate is only half sweet, and semiannual sales happen twice a year.
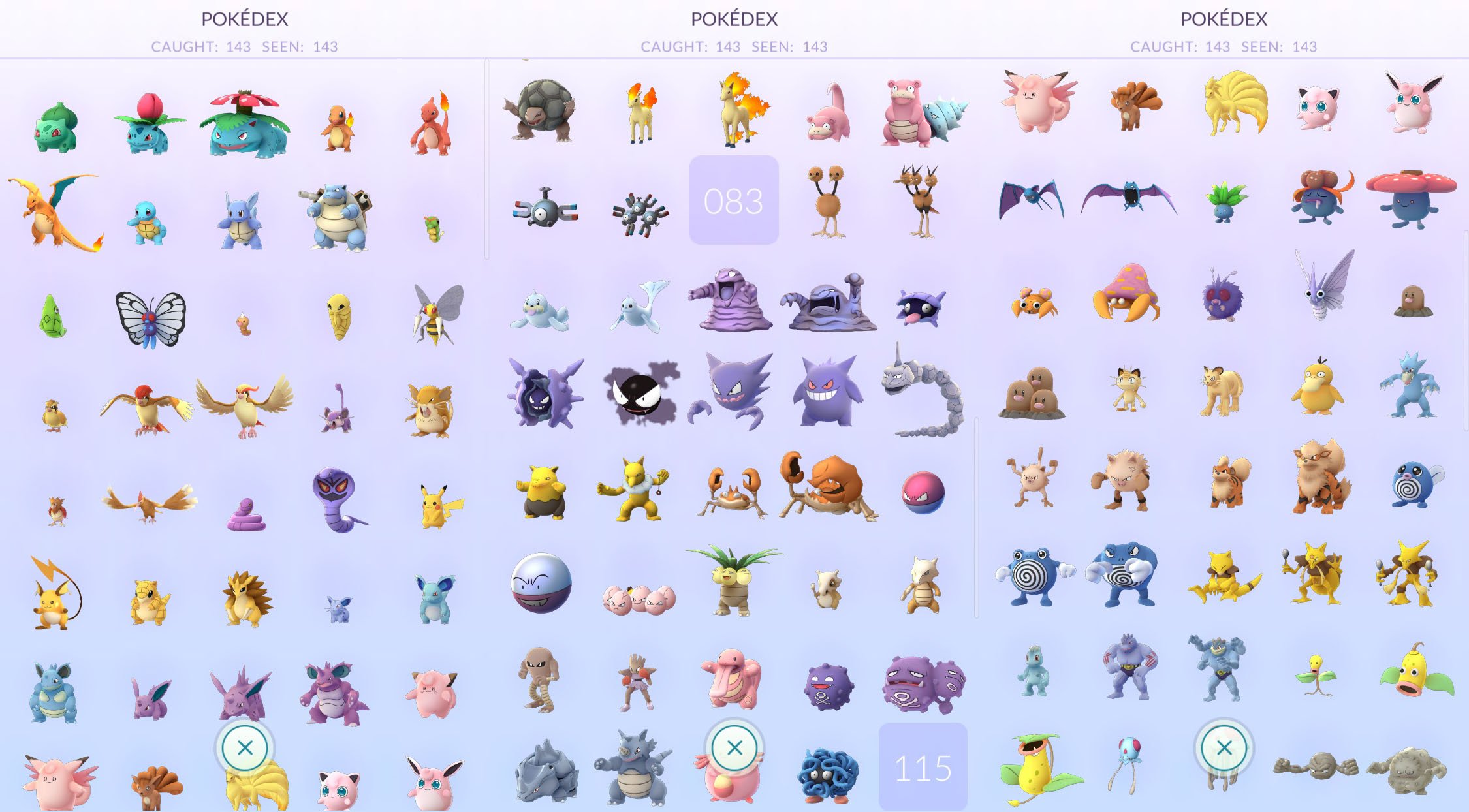
read moreWhy You Should Have Trust Issues with Pokemon Go, and Every Other App on Your Phone
July 13, 2016
Viral Game Highlights Calls Attention to Timeless Security Debate
I want to run into traffic, fall into a pond, catch Pokémon while my wife is in labor, and find a dead body; let’s check out this Pokémon Go thing!
Pop quiz: Is this a valid login screen for Google Account services? This is the first screen I see when I click login with my Google Account from Pokémon Go. It’s concerning because it offers no clear indication this is a valid page, no way for me to verify that I’m sending my credentials to Google, no SSL/TLS lock, and no security controls – just a white page that looks pretty legit.
read moreIn Defense of Reverse Engineering and Responsible Disclosure
September 3, 2015
I was pretty disappointed after reading Mary Ann Davidson’s blog post discouraging customers from reverse engineering their software for any reason. As CSO of Oracle, one of the largest software providers in the world, I expected her thoughts on security researchers and responsible disclosure to be more enlightened. Instead I saw a glib response that echoed sentiment from the turn of the last century.
The post has since been removed from Oracle’s official blog, which shows that while this may be their internal policy and thinking, the company understands it isn’t popular to hold such opinions.
read moreRuby open allows command injection if user controlled
June 3, 2015
We’ve been getting a lot of Ruby on Rails Penetration tests and code reviews at Security Innovaiton, and I’ve been writing a decent amount of it myself. In general it’s a great framework, but like any other framework there are a few little gotchas that could lead to a security vulnerability. A colleague of mine, Arvind, wrote a great blog post on the Security Innovaiton blog in which he outlined a few of these check that out here.
read moreNew Mac Install Guide
November 8, 2014
This guide may help you install some required and some helpful settings on a new mac. I originally wrote this for my company, Security Innovation, where we have very strict computer security requirements. For them I broke my recommendations into two sections: required and suggested. Everything in the required section is well, required, for the SI policy. Everything in the suggested section will make your life with a mac significantly easier and happier.
read moreUnderstanding Customer Needs and Helping Them Mature
September 22, 2014
(Originally posted on the Security Innovation Blog)
##Security Innovation’s manifesto on being a trusted advisor
Each client has different backgrounds as well as a different depth of knowledge, experience, comfort, maturity, and trust. As trusted security advisors with genuine and heightened passion for helping our clients fundamentally improve their processes and build internal expertise, we take pride in delivering customized solutions that meet each company’s needs. At its core, this goes beyond simply setting and meeting expectations reliably.
read moreMy Experiences with IOS8 and Yosemite so far
July 26, 2014
I’ve been running iOS8 and Yosemite for a while now, (since early beta, actually). There were some real challenges in the early betas, but the latest version is pretty solid, but the new “cool” features aren’t quite there yet.
###OSX
Spotlight - moved to the center of the screen and more powerful. Can do calculations and conversions, can see previews and perform some actions Safari - I don’t use this, but there seems to be some updates Mail - essentially the same, maybe a little faster?
read moreThe Importance of Vulnerability Disclosure Programs and Bug Bounties
June 5, 2014
I’ve written before about how important responsible disclosure is for Security Researchers. That responsibility falls on both sides of the discussion. Of course it falls on the side of the security researcher. When they find a security vulnerability they should work with the company to disclose it properly and to make sure it’s fixed properly. They should do this for free and without extortion. I think most professional security researchers are on the same page, and while we may debate whether it’s prudent to ever publicly disclose an issue, most of us will try to use responsible disclosure first.
read moreMy New Record Player and Beck - Morning Phase (The Vinyl Experience)
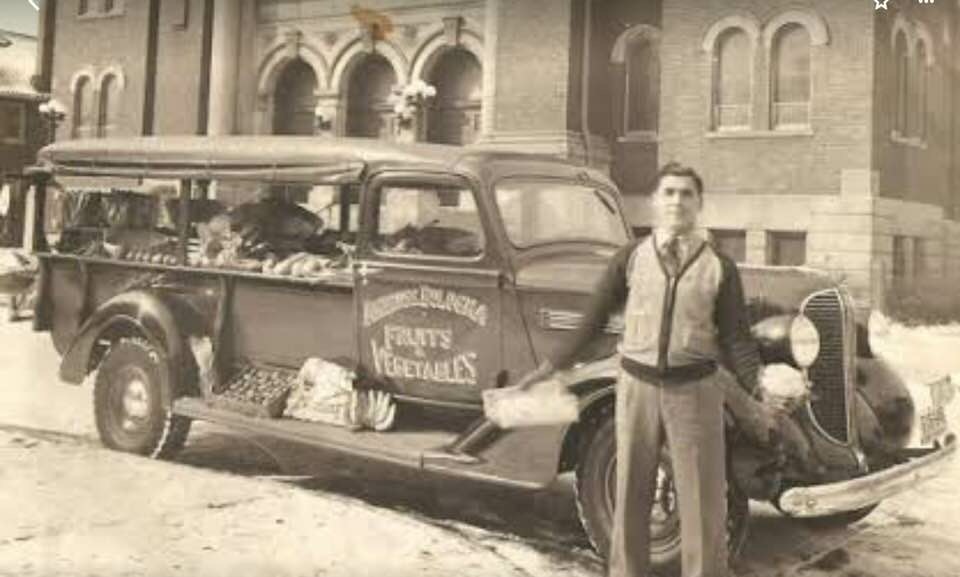
March 27, 2014
I’ve wanted a record player for years now, finally after listening to me hem and haw about it my wonderful wife, Katherine, bought me a fantastic player for my birthday. I’ve been scrambling to build a record collection ever since and it has been wonderful.
I haven’t done a fully blind test, but I do enjoy the physicality and process of the record over simply selecting a song from a playlist or iTunes album.
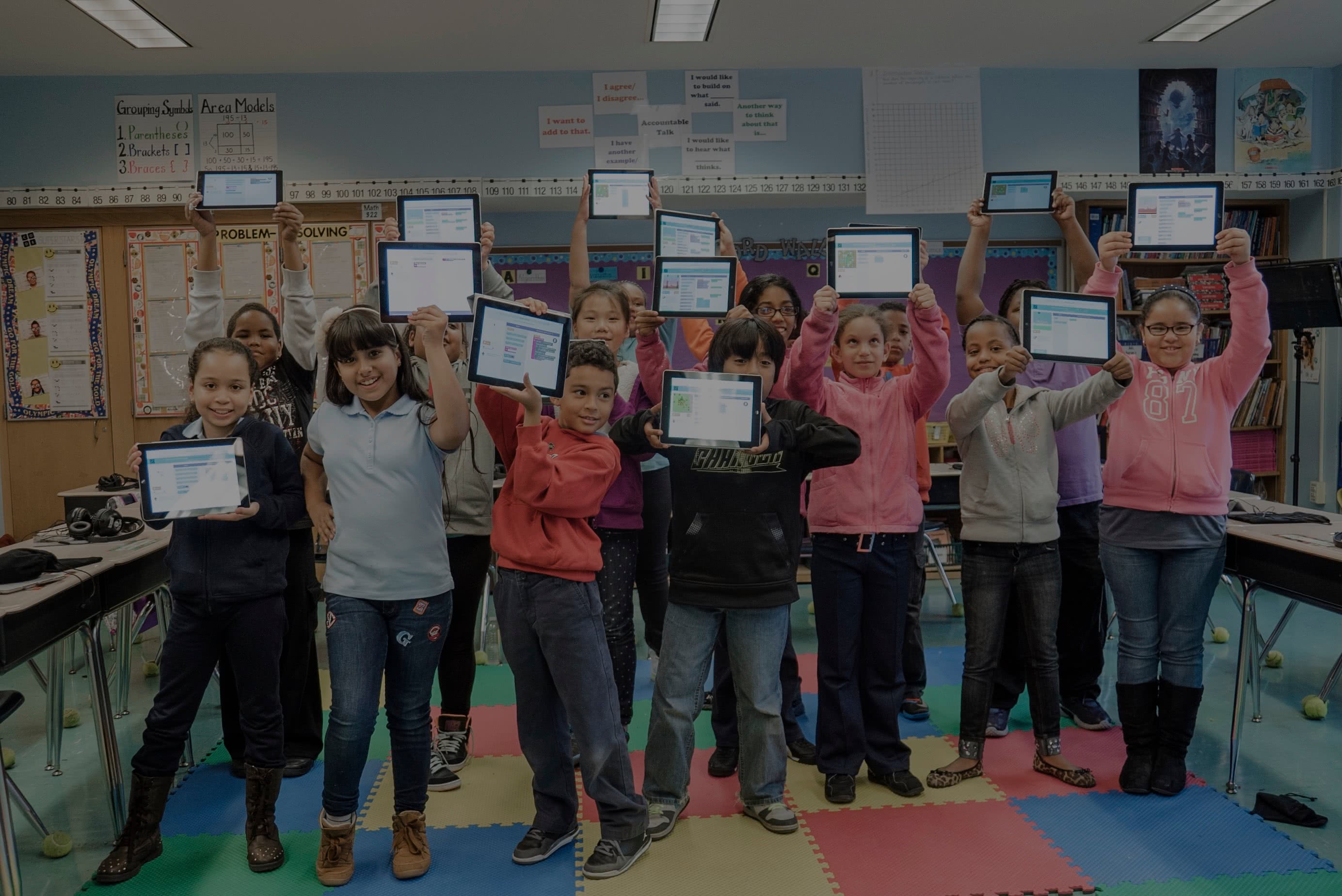
read moreAn Hour of Code with Code.org
December 14, 2013
I am staggered and truly impressed by what the team at Code.org has accomplished in such a short period of time.
When Hadi Partovi started conversations in May of this year with Technically Learning to merge our organizations he had huge goals: to get Computer Science into every school, to teach every american student how to code, and to do all of this in months, not years. We were, understandably, a bit skeptical, but Hadi has the credentials, passion, vision, and resources to accomplish great things.
read moreGmail Changes to Displays Images by Default
December 12, 2013
Gmail recently changed the way it displays images to you (Official Gmail Blog). From a user perspective this can be good, from a security perspective this might be good, from a privacy perspective I’m not convinced this is a good move for the sender or recipient. First let me explain what changes Google has made and how it affects you.
Usually when you receive an image embedded in an email you’ll see a bar at the top of the email letting you know that there are images in this e-mail, but that they haven’t been displayed.
read moreWhy I Donated to Help Jailbreak iOS7 & You Should Too
December 4, 2013
There are almost always multiple sides to any debate in software security. For that reason I find myself saying “It depends” far more than I may expect. I came across isios7jailbrokenyet.com a couple days ago and the question of whether this would help or hurt security popped into my mind. This debate, like many others is worth digging into:
Is Open Source more secure than Closed Source? It depends Is Windows more secure than Linux?
read moreEmail Strategy
November 24, 2013
I’ve seen a few different articles about people’s different e-mail strategies and they certainly seem to be a hot topic. With our ever reliance on e-mail as a primary mechanism for communication it’s important to be able to keep up with the constant stream of messages coming in.
You ultimately have to devise a strategy that works for you, and there are many out there already, I’ll be throwing my hat into the ring.
read moreShutdown
October 3, 2013
My mom loves the NASA channel. She has it on all the time in the background at her house and when Dragon docked with the International Space Station I got a minute by minute update. I think NASA is awesome too, so when she sent me an e-mail last night asking why the NASA channel was down, it a nerve already rubbed raw by our congress failing to do their jobs.
read moreAnatomy of a Distributed Denial of Service (DDoS) Attack
April 3, 2013
The recent wave of DDoS attacks on banking web sites, and the Spamhaus DDoS attack (which was three to five times greater than the biggest attacks against U.S. banks) is reinforcing that, while the attacks aren’t particularly sophisticated, they do warrant our attention. If targeted the attacks can be extremely disruptive to online operations. To protect against DDoS attacks, it’s important to understand their root cause.
DDoS’s take many forms but at the core, they’re essentially a battle of resources.
read moreNASA Forced to Suspend All Public Outreach & Education Programs
March 23, 2013
Yesterday was a sad day for NASA who were forced to halt all education and public outreach activities including public engagement out outreach events, programs, activities and products. These spending cuts, enacted by congress through inaction will directly affect the education, inspiration, prosperity and competitiveness of our future generations of the USA (India and China are both investing heavily in space exploration programs). We just reduced our investment in space exploration from 1/2 of one cent!
read moreJoe_CMS Open Source!
November 8, 2012
I’m happy to say that tonight I’ll be publishing JoeCMS as a free and open source (GPL), as evidenced by the little “Fork me on GitHub” banner in the upper right corner of this page. JoeCMS runs this website and a couple of others and I’ve been really happy with its simplicity and feature set. I created JoeCMS after trying to shoehorn a few of the bigger CMS’s into my needs.
read moreMobile Application Security Testing FAQs: Post #1
August 20, 2012
A couple weeks ago I presented a webcast at Security Innovation that covered techniques for testing mobile applications. As usual I was long winded with stories and analogies and went over time. I tried to answer as many questions as possible, but we had to cut the webcast off at ten minutes after the hour. As I closed out the webcast I mentioned that there were dozens of great questions that I wanted to answer, but didn’t have time for.
read moreHow Much Security Does Obfuscation Get You?
July 5, 2012
In November of last year engadget ran a story explaining how easy it was to decompile Windows Phone 7 applications. A lot of developers were surprised that their apps could be reverse-engineered and decompiled and attackers could easily browse the source of their applications. The attack goes something like this: download ILSpy for Free, Sync your Windows Phone 7 or download a Windows Phone 7 App to your computer, open the app in the Reflector, right click and select “decompile.
read moreWhy Privacy Matters Even if You Have 'Nothing to Hide'
June 29, 2012
I just read a really well written article by Daniel J. Solove is a professor of law at George Washington University who says we should stop thinking about privacy in Orwellian terms (nothing to hide), but in Kafkaesque terms (if we have enough information about you we will be able to find something, eventually).
I think this is especially pertinent in this new age of surveillance and data storage. It costs nearly nothing to store information now, especially for large corporations and governments so they have very little incentive to purge surveillance data.
read moreWhat LinkedIn Should Have Done with Your Passwords
June 6, 2012
By now, you’ve probably heard that LinkedIn’s passwords have been allegedly compromised. I first heard about this from a Norwegian website earlier today. Here is what we know now:
LinkedIn has not confirmed the leak and currently doesn’t understand how the hack could have happened, but there is a 271 MB file of alleged SHA-1 hashes floating around with LinkedIn’s name on it. The hash digests are unsalted SHA-1 hashes.
read moreConstant Vigilance
May 21, 2012
I’ve been in the Security Industry for about ten years now. I say that not to brag, but to give context for the rest of this post. I’ve assessed countless pieces of software of nearly every type, web apps, web services, desktop, firmware, mobile, Operating Systems, and more. So believe me when I say this is a bit of a tough post to write.
Up until about a month ago Joe_CMS had a major security vulnerability in it.
read moreBoeing Paying Hackers to Break into Their Systems
May 14, 2012
Boeing’s systems need to be capable of staving off hackers, and for more than two years, the company has employed two “hackers” to test the security of its computer systems. I like it, but there’s more that needs to be done.
Since most large organizations rely on a mix of COTS hardware, 3rd party software applications, communication technologies, and custom code to run their IT infrastructure, it’s difficult to apply a single security assessment solution to ensure adequate coverage and protection.
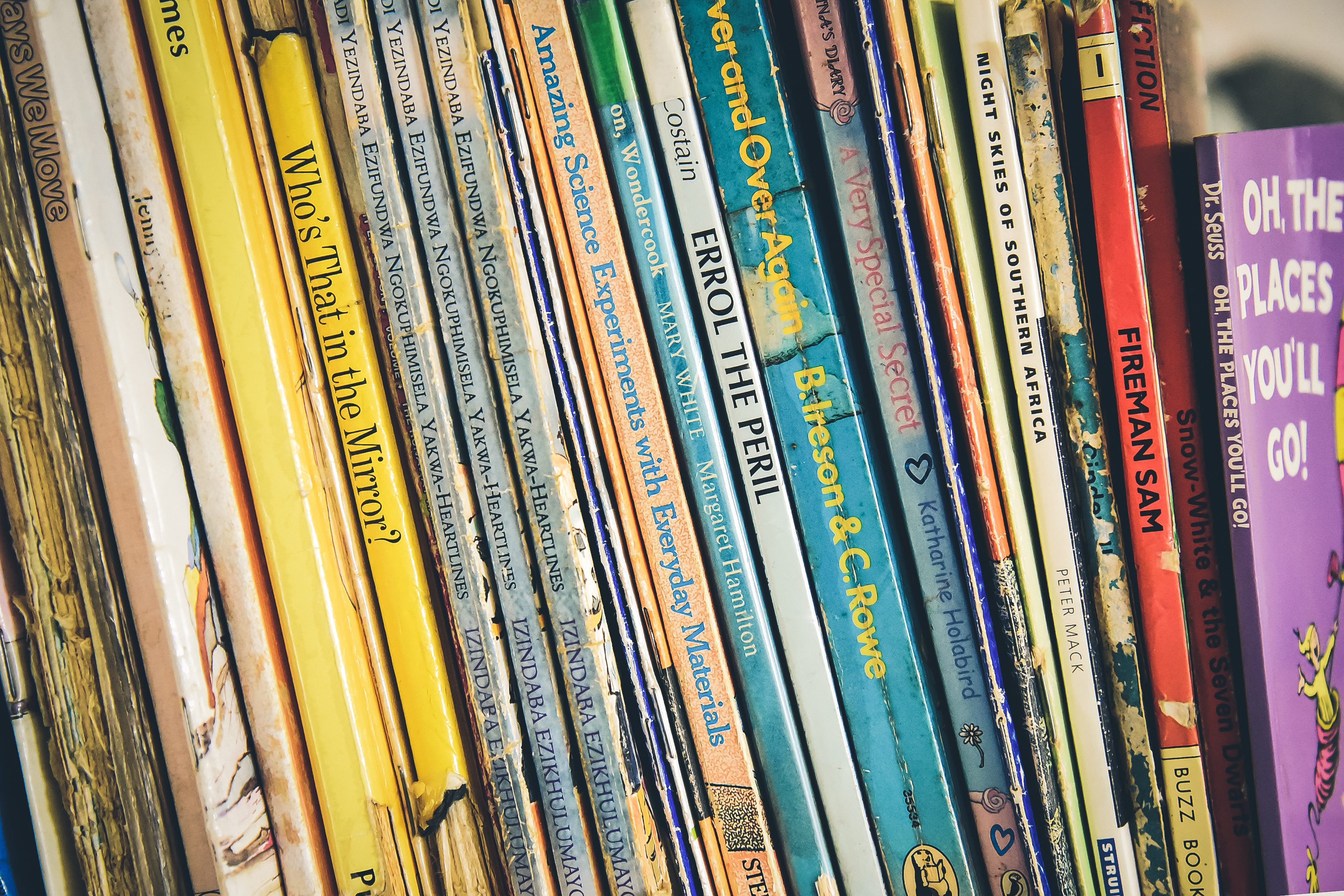
read moreMy Reading Cycle
May 7, 2012
I don’t read a lot, but over the last few years I’ve developed a book choice cycle that works really well for me. It helps me finish challenging books that I want to read for development, and entices me to be selective about the “fun” books I burn through. My reading cycle is: one “fun” book, one personal development book and one professional development book.
My first book can be something fun.
read moreDeveloping Tools for Professional Hackers
April 30, 2012
Professional hackers or security testers tend to write a lot of code. We write exploit code, fuzzers, code to handle esoteric protocols and data structures, unpackers, disassemblers, reversers, parsers, and so much more.
We write this code because often what we’re doing is so specific that is requires one off tools. Over time we develop an enormous arsenal of our own tools, scripts, functions and code snippets that make us significantly more efficient, but are hacks that are only beneficial to us.
read moreFinding Your Inner Evildoer (4/4): An Evil Streak
April 23, 2012
We’ve made it to the last part of my four part series on what makes a great security tester or hacker. Even though this fourth piece is what I consider to be the most important and exciting quality of a hacker, I do recommend you go back and read the first three pieces of the series. In part one I gave An Overview of the qualities I look for in the next great security tester.
read moreFinding Your Inner Evildoer (3/4): A Good Imagination
April 16, 2012
In my previous posts I talked about what an overview of what makes a great security tester, and in depth about what it means to have complete knowledge of the system. If you haven’t read those yet, I suggest you do so now, that’ll help set the stage for the following post.
A great imagination extends beyond the ability to imagine a system as it could be, but extends to envision the truly interesting bugs and vulnerabilities in a system.
read moreWhen to Rebuild Your Process from Scratch
April 9, 2012
A few months ago I had the opportunity to rebuild the way we operate the services branch of our company. If you’re not familiar with my background I lead a team of the security consultants to help software companies reduce their overall risk in relation to hackers and data breaches by performing software security assessments.
Security Innovation is a very dynamic company, we are still relatively small (although medium to large if you compare us to other companies in the industry) and full of very, very smart individuals who can be trusted to do the right thing no matter what.
read moreFinding Your Inner Evildoer (2/4): Complete Knowledge of the System
March 31, 2012
In the previous post I described an overview of the three traits I look for in great security testers: Complete Knoweldge of the System, A Good Imagination, and An Evil Streak. In this post I describe, in detail, what I mean by the first trait, “Complete Knowledge of the System.”
The first thing I look for in an awesome security tester is deep knowledge about everything that goes on in a computer system.
read moreContinuous Incremental, Personal Improvement
March 22, 2012
I am an optimizer. I try to optimize nearly everything in my life. This, I think, is why I tend to spend so much time on personal productivity, time management and other personal optimization techniques.
My theory, which should be an undercurrent of your thinking, was that often times we pick goals that are too large and fail because of our lack of perceived progress. If we choose small aspects of our lives to improve upon we will see our progress more quickly which will tighten the positive feedback loop to increase the likelihood that we will attempt an improvement project again.
read moreFinding Your Inner Evildoer: Part 1
March 14, 2012
As a Security Tester, or hacker, I have one of the most exciting and creative jobs in the industry. We are asked to find as many critical security vulnerabilities in complex software systems with limited resources - before the application is released or shipped. We have the challenge of knowing more about the system in the first couple of days than the developers who wrote the system. We have to find every vulnerability in the system, the attacker effectively has all the time and resources in the world to find only one issue.
read moreCISCO Password Revealer
March 12, 2012
I haven’t had much luck with any CISCO clients on the mac. Inevitably clients will send me a CISCO profile configurations that I can’t easily use on my mac. I went searching for a tool that would reverse the encryption on the file so I could use raw values (Username, UserPassword, GroupName and GroupPassword) in the built-in Mac VPN client. I found this app a while ago, built in 2005 by the “EvilScientists.
read moreBattling with Word and Excel
February 28, 2012
I recently had to build a word document that references fields in an excel spreadsheet. Since this report will update over time from data in the spreadsheet I wanted it to pull in the live data from excel and use it inline. Kind of like “Our annual sales numbers for 2011 were {SalesFromExcel}”
I pasted the items into the doc but they would always bring a line break before and after the data.
read moreWhich is More Secure: Windows or Linux?
July 29, 2011
Somebody on LinkedIn asked the above question to a group I'm part of. I decided to answer it thinking "Oh, I can chime in with a quick little answer", but the more I wrote the more complex the answer became.
Here is my response:
I think the question is far more complex right now actually. For example, what constitutes "Linux" or "Windows"? If we're talking only about the kernel, then they're about the same (both extremely secure).
read moreThe High Cost of an Application Security Data Breach
June 30, 2011
In the wake of the Sony Security Breaches (breaches, you say? As in plural? Yes, read on for more information) I decided to update some of our instructor led training slide decks
The first few slides of our security awareness courses include a number of slides intended to scare people into paying attention to the threat of security issues. We do this by showing the largest, most costly and most impactful data breaches and security vulnerabilities in recent history.
read moreUsing the ConfigurationManager to Access your ConnecitonStrings in the Web.Config
April 25, 2011
This is just a quick post because I couldn’t find this information easily available on other sites. I knew there was a quick way to access the connection strings from the web.config file (and other app settings) without going through some crazy XML reader or doing something ridiculous like what http://msdn.microsoft.com/en-us/library/ms178411.aspx. I’m sure this is on the internet somewhere, but the more places the better as far as I’m concerned. If you simply add the System.
read moreNew WikiRater Features
April 18, 2011
I’ve been working to add a few more features for WikiRater that I think are really cool. The one that I’ve had the most fun with so far is the “Trending Article” page. This page shows articles that are being rated right now. It works pretty similarly to reddit or hacker news, if you’re familiar with them.
The other fun feature is the Random Interesting Article. This will find an article with an average rating of 8 or higher.
read moreWhen is it OK to Build up Technical Debt
December 31, 2009
As I previously mentioned I’ve been writing a bit of Ruby on Rails. I’m surprised at how quickly I can slap something together and get results, especially prototypes, up and running quickly. Technical Debt is generally defined as the eventual consequence of building software in a quick and dirty way. This most commonly occurs when a developer jumps directly into writing code without architecting or thinking through the solution. Usually a solution is spit out prematurely and will quickly fall over under heavy load or stringent testing.
read moreTime Management with the Pomodoro Technique
October 8, 2009
About 6 months ago it seemed like the internet was infatuated with a new time management technique called “Pomodoro.” Developed by Francesco Cirillo, The Pomodoro Technique is a good way to increase focus, manage time and improve time estimations. If you’re curious, the term “Pomodoro” comes from the Italian word for tomato, which is the type of kitchen timer the author of the technique used to time his sessions, more on this later.
read moreManage Energy Not Time
October 2, 2009
Recently I was forced to work only 6 hours per day. On the surface this seems great, I immediately started filling my time with other things that I’ve wanted to get around to, but never felt I had the time for because of my busy 10-12 hour per day work schedule. That excitement quickly moved way to fear, fear not getting as much done, fear of losing clients or projects due simply to not having enough hours to work in a day.
read moreGoals, Results and Activities - defining your productivity
August 16, 2009
I think that it is important to properly define the terms that we use when talking about productivity. Since these words are somewhat subjective it matters more that you have a specific definition that you can refer to periodically than to agree with everybody else on the specific terms and definitions.
I use the words Goals, Results and Activities.
A quick definition might be that a Goal is a long-range target.
read more